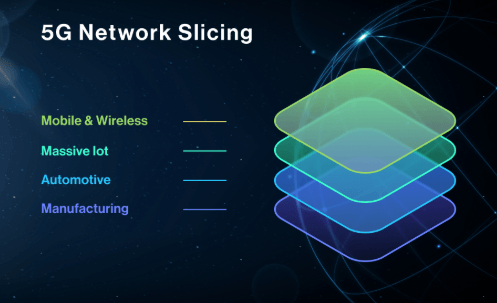
Network slicing in 5G enables multiple virtual networks to run on a common physical substrate, each tuned to specific service requirements. Slices are defined, allocated, and managed through programmable orchestration to meet distinct latency, throughput, and isolation targets. The approach supports end-to-end QoS and security differentiation, with lifecycle policies and auditable controls to prevent cross-slice leakage. The practical implications for performance and risk warrant careful consideration as governance and implementation details unfold.
What Is Network Slicing in 5G?
Network slicing in 5G refers to the logical segmentation of a single physical network into multiple, independent virtual networks, each tailored to specific requirements. It enables differentiated service parameters, resource isolation, and policy adherence. The mechanism supports latency guarantees and QoS differentiation. Isolation strategies prevent cross-slice interference, preserving performance boundaries, while architectural flexibility permits rapid adaptation to changing traffic profiles and diverse application needs.
How Slices Are Created and Orchestrated
The creation and orchestration of slices involve mapping service requirements to a virtualized network fabric, followed by the allocation and management of resources across multiple domains.
In this process, programmable controllers coordinate northbound and southbound interfaces, enforcing latency tradeoffs and isolation guarantees, while dynamic placement and scaling ensure deterministic performance, cross-domain consistency, and policy-compliant lifecycle management for each slice instance.
Use Cases: Why Slicing Impacts Performance and Security
Use cases illustrate how network slicing directly affects end-to-end performance and security postures by isolating traffic, tailoring QoS, and enforcing domain-specific security policies. In practice, tailored slices provide predictable latency guarantees and reduced cross-slice interference, enabling mission-critical services and diverse apps to operate with defined performance benchmarks. Security isolation limits blast radii, confining breaches and preserving user transparency and trust.
Choosing and Managing Slices: Practical Guidelines
Selecting and operating slices in a 5G environment requires a structured approach to balance performance, isolation, and management overhead.
The guidelines emphasize disciplined lifecycle management, clear SLAs, and preconfigured guardrails.
Practical focus covers latency budgeting, resource partitioning, and dynamic reconfiguration.
Privacy guarantees hinge on strict policy enforcement, secure telemetry, and auditable isolation to prevent cross-slice leakage and ensure predictable service quality.
See also: Neuromorphic Computing Explained
Frequently Asked Questions
How Does Network Slicing Impact Edge Compute Placement Decisions?
Network slicing influences edge compute placement by guiding edge orchestration through dynamic latency budgeting, allocating resources to meet SLA targets; decisions balance isolation and shared infrastructure, optimizing placement across slices while preserving performance, security, and flexibility for edge workloads.
Can Slices Be Migrated Across Different 5G Vendors Seamlessly?
Cross-vendor compatibility is limited; seamless slice migration across 5G vendors remains constrained by proprietary interfaces and governance. Juxtaposed with open standards, lifecycle governance emerges as critical for policy, orchestration, and reliability, enabling controlled, freedom-centered cross-vendor adaptation.
What Are the Regulatory Constraints for Cross-Border Slice Sharing?
Regulatory constraints limit cross border slice sharing, impacting edge compute placement decisions and vendor interoperability for seamless migration; data plane and tenant isolation must satisfy QoS metrics under extreme load, aligning governance with data localization preferences.
How Is Tenant Isolation Enforced at the Data Plane Level?
Data plane enforcement ensures tenant isolation via per-tenant queues and flow rules, coupled with edge compute proximity; slice placement and QoS metrics mitigate extreme load, while regulatory constraints impact cross border sharing during cross vendor migration.
What Metrics Guarantee Qos During Extreme Network Load?
Latency guarantees and QoS metrics are tracked under extreme load, prioritizing critical slices; statistical multiplexing, scheduler discipline, and admission control enforce bounded delays, while congestion indicators expose resilience limits and guide proactive resource reallocation.
Conclusion
Network slicing in 5G enables multiple virtual networks on a shared physical base, each with tailored performance, latency, and security policies. The orchestration layer ensures end-to-end isolation, policy enforcement, and auditable stewardship across domains. One notable statistic: operators report up to 40% faster service provisioning when automated slice orchestration is employed, illustrating how programmability and strict lifecycle management translate into predictable, low-latency outcomes. This precision underpins reliability for mission-critical and high-throughput applications alike.